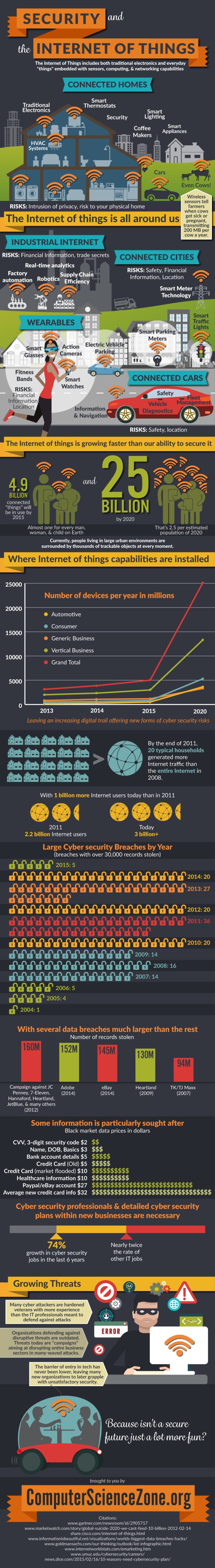
I was invited by ComputerScienceZone to share this fascinating infographic on my site – so here it is – a fascinating insight into the diversity and number of “things”, combined with the risks associated with the rapid growth and poor security.
Tag Archives: data privacy
EU versus Google – £12 million DPA fine
 The pressure on Google over European data privacy issues has been ongoing for several years as EU data protection watchdogs attempt to bring the organisation – and other huge US companies – into line with European data protection principles.
The pressure on Google over European data privacy issues has been ongoing for several years as EU data protection watchdogs attempt to bring the organisation – and other huge US companies – into line with European data protection principles.
The latest threat to Google comes from Holland, where the Dutch DPA has threatened Google with a fine of up to 15M euros for breaking local laws over how it can use user data. Google has been given until the end of February 2015 to change the way it handles personal data, before the fine is levied.
Online behaviour used to target advertising
So what has Google done wrong? The issue is over the way Google uses data about people’s online behaviour to tailor advertisements. Google builds up a profile for every one of its users based on keywords used in searches, email messages, cookies, location data – even video viewing habits. However, it does not inform its data subjects that it is collecting and using data in this way, and nor does it obtain consent.
Google’s Data Assets
Google’s data is a core asset for the business, and other businesses like it. One of Google’s key data privacy issues is that the company has merged all its separate privacy policies into one policy which allows Google to share its user data across all its services – for example, Gmail data and search engine data can be used and combined across the company. In addition, there is no opt-out for the data subject.
From Google’s point of view, its customer profiling is enhanced considerably by this activity – and advertising to targeted customers is Google’s core revenue stream. Google also uses customer data to drive new products such as Google now (appointment based app, giving details on how to get to your appointment, where it is, what are the traffic conditions and what time to leave) – a great concept, but one that would be useless without Google’s ability to collect and use data from its users.
It has been clear for some time that the EU is determined to take on the challenge of the giant UK search engines and social media platforms, and curb the way they use data. Because Google has such a vast share of the market, it, in particular, regularly comes under fire from the EU.
Google Privacy Policy – Fairness and Transparency
The requirement for additional permissions or opt-outs may be more problematic than helpful for Google customers. But fairness and transparency is an issue that Google could address relatively simply – as a minimum the customer should be informed about the data Google is collecting about him or her, why it is being collected and how it is being used. And a little bit of creativity in the wording would serve to illustrate the benefits to the customer.
The single privacy policy makes such transparency difficult. So perhaps the simplest solution is to re-establish separate privacy policies for each of its business areas. That might at least serve to reassure not only the EU, but also the US data protection authorities who have also expressed concerns over Google’s single privacy policy.
Your thoughts and views are always welcome – please add your comments below. If you have any concerns about your data compliance in general or the impact of EU changes in your business, contact us on 01787 277742. Or email victoria@datacompliant.co.uk
EU Data Protection Regulation – Getting closer?
 The EU Regulation is designed to replace the current multiplicity of EU data protection laws with a single set of rules to be applied throughout all Member States. Time is moving on so it’s important to keep on top of the discussions and updates being published.
The EU Regulation is designed to replace the current multiplicity of EU data protection laws with a single set of rules to be applied throughout all Member States. Time is moving on so it’s important to keep on top of the discussions and updates being published.
Last month’s proposed revisions to Chapter IV (which deals with data controller and data processor obligations) are summarised below. However, it is worth remembering that “nothing is agreed until everything is agreed” in relation to the Regulation.
Greater discretion for data controllers – risk-based compliance
Businesses will be relieved to see greater discretion for data controllers in complying with the legislation as recent Chapter IV discussions in Europe have moved towards a risk-based approach to compliance.
A balance between privacy and entrepreneurship
 The proposed amendments to Chapter IV suggest that data compliance obligations should be proportional to the organisation’s specific data processing activity and associated risks.
The proposed amendments to Chapter IV suggest that data compliance obligations should be proportional to the organisation’s specific data processing activity and associated risks.
Once these activities and risks have been assessed, appropriate privacy and data protection tools should be instigated by the organisation.
Different activities, even where the same data is involved, may quite often have different consequences, requiring different levels of protection. The risk-based approach allows data controllers a more flexible approach in assessing their data compliance responsibilities within the context of their own particular business.
It appears that most countries welcome the risk-based approach, which they view as providing a good balance between protecting personal data and safeguarding businesses and entrepreneurship.
Chapter IV Proposed Revisions
Below are some examples of the revisions proposed by the EU Council:
- Data protection impact assessments are only required where “high” risk (for example identity theft, fraud or financial loss) to the rights and freedoms of individuals is involved
- The appointment of Data Protection Officers is voluntary (unless individual Member State legislation states otherwise)
- Only data breaches that are likely to result in “high risk for rights and freedoms of individuals” need be reported
- If stolen or breached data is encrypted or protected in such a way that the data remains indecipherable, there is no requirement to report the breach.
- Required levels of security measures will be established by considering multiple factors, including the nature, scope, context and purpose of the data processing to be undertaken, in combination with the cost of implementation and the technology available.
- Only where a data privacy impact assessment indicates that data processing would result in “high risk” to the rights and freedoms of individuals, the supervisory data protection authority should be consulted prior to the start of such processing
There is also a suggestion that data controllers may use “adherence of the processor to an approved code of conduct or an approved certification mechanism” to demonstrate compliance with the obligations of a controller. So organisations may find it well worth considering selecting only those data processors who have appropriate data security certification such as ISO 27001 or DMA DataSeal.
If you have any concerns about your data compliance in general or the impact of EU changes in your business, contact us on 01787 277742. Or email victoria@datacompliant.co.uk

CCTV Data Protection Guidelines from ICO
 Clearly surveillance has both benefits and drawbacks, and the level of public interest and debate about both is increasing. Technology is advancing swiftly, and surveillance cameras are no longer simply passively recording and retaining images. They are now also used proactively to identify people of interest, to keep detailed records of people’s activities both for social (eg schooling, benefits eligibility) and political (eg terrorist) reasons.
Clearly surveillance has both benefits and drawbacks, and the level of public interest and debate about both is increasing. Technology is advancing swiftly, and surveillance cameras are no longer simply passively recording and retaining images. They are now also used proactively to identify people of interest, to keep detailed records of people’s activities both for social (eg schooling, benefits eligibility) and political (eg terrorist) reasons.
There’s a real risk that, despite the benefits, use of CCTV can be very intrusive.
The ICO’s new CCTV code of practice continues its focus on the principles that underpinned the previous code of practice. However, it has been updated to take into account both the changes in the regulatory environment and the opportunities to collect personal data through new technology.
There is some fascinating information in the guidelines – specifically around some of that new technology, where three of the key recommendations are:
- Privacy Impact Assessments – a requirement that involves ensuring that the use of surveillance systems is proportionate and addresses a pressing need (see the
- Privacy Notices / Fair processing – a key issue for many of the new technologies is finding creative says of informing individuals that their personal data is being processed – particularly where such processing is simply not obvious.
- Privacy by design – for example, the ability to turn the recording device (audio and / or sound) on and off as appropriate to fulfil the purpose; the quality must be high enough to fulfil the purpose; the use of devices with vision restricted purely to achieve the purpose
The new technology specifically covered in the guide includes:
Automatic Number Plate Recognition (when to use it, data storage, security issues, sharing the data and informing individuals that their personal data is being processed – something of a challenge needing some creative thinking);
Body Worn Video (warnings against continuous recording without justification; the use of BWV in private dwellings, schools, care homes and the like – and, again, the thorny issue of informing subjects that they are being recorded);
Unmanned Aerial Systems drones are now increasingly used by businesses as well as the military (Amazon has stated its intention to use drones to deliver parcels …). Some of the key issues are privacy intrusions where individuals are unnecessarily recorded when the drone has some other purpose; the distinction between domestic and commercial use; providing justification for their use; the ability to switch the recording system on and off; the whole system of data collection, storage, accessibility, retention periods and disposal requires compliance.
Automated recognition technologies are increasingly used commercially to identify individuals’ faces, the way they walk, how they look at advertising and suchlike. Again, the issues of fair processing, degree of accuracy of images and their identification, storage, retention, transfer, disposal and security are all key to compliance.
If you are using surveillance devices to view or record and / or hold information about individuals, then it’s worth noting that such use is subject not only to the Protection of Freedoms Act (and its Surveillance Camera Code of Practice), and the Data Protection Act, but you also need to consider your obligations under The Freedom of Information Act 2000 and the Human Rights Act 1998.
If you have any concerns about your data compliance in general or your surveillance camera compliance specifically, contact us on 01787 277742. Or email victoria@datacompliant.co.uk

Surveillance Camera Code of Practice – 12 Principles
 Do you use a surveillance camera system within your organisation? If so, it’s worth noting that the Surveillance Camera Code of Practice must not only comply with the Data Protection Act and its 8 Principles, but also provides its own 12 guiding principles:
Do you use a surveillance camera system within your organisation? If so, it’s worth noting that the Surveillance Camera Code of Practice must not only comply with the Data Protection Act and its 8 Principles, but also provides its own 12 guiding principles:
- Purpose: Use of a surveillance camera system must always be for a specified purpose in pursuit of a legitimate aim, and necessary to meet an identified pressing need
- Privacy Impact: Use of a surveillance camera system must take into account its effect on individuals and their privacy, with regular reviews to ensure its use remains justified
- Transparency: There must be as much transparency in the use of a surveillance camera system as possible, including a published contact point for access to information and complaints.
- Accountability: There must be clear responsibility and accountability for all surveillance camera system activities including images and information collected, held and used.
- Policies and procedures: Clear rules, policies and procedures must be in place before a surveillance camera system is used, and these must be communicated to all who need to comply with them
- Relevance and Retention: No more images and information should be stored than that which is strictly required for the stated purpose of a surveillance camera system, and such images and information should be deleted once their purposes have been discharged
- Access to retained images and information should be restricted. There must be clearly defined rules on who may gain access for what purpose; the disclosure of images and information should only take place where it is necessary for such a purpose or for law enforcement purposes
- Standards: Surveillance camera system operators should consider any approved operational, technical and competency standards relevant to a system and its purpose, and work to meet and maintain those standards
- Security: Surveillance camera system images and information should be subject to appropriate security measures to safeguard against unauthorised access and use.
- Audit: Effective review and audit mechanisms should be in place to ensure legal requirements, policies and standards are complied with in practice. Regular reports to be published.
- Public Safety: When the use of a surveillance camera system is in pursuit of a legitimate aim, and there is a pressing need for its use, it should then be used in the most effective way to support public safety and law enforcement with the aim of processing images and information of evidential value.
- Accuracy: Any information used to support a surveillance camera system which compares against a reference database for matching purposes should be accurate and kept up to date.
If you have any concerns about your data compliance in general or your surveillance camera compliance specifically, contact us on 01787 277742. Or email victoria@datacompliant.co.uk

Data Protection and the ICO
Data Protection Complaints 2013 – 2014
Yesterday I read that the Information Commissioner’s Office handled 259,903 calls to its helpline and has resolved 15,492 data protection complaints last year. This is an increase of 10% over the previous year. And here’s another staggering figure – the ICO received 161,720 reports from people about spam texts and nuisance calls.
Half the total complaints received related to “subject access”, with a range of organisations about whom complaints were made, including lenders, local government, educational providers and local health providers.
The importance of data protection in business
Organisations and businesses can no longer ignore the importance of data protection governance, compliance and security – they now have no choice but to understand and meet their regulatory requirements to avoid the penalties of non-compliance. Last year’s attitude to and handling of ‘subject access requests’ is a perfect illustration of the current complacency seen among some data users.
The sheer volume of personal data being collected physically and digitally every day is multiplying at an extraordinary rate and organisations are continuing to find ever more complicated ways of using data. Use of big data continues to develop with organisations trying to navigate their way through woefully outdated legislation.
The importance of the ICO
As a result, the data protection challenges to business, the consumer and the ICO are spiralling. It’s increasingly important for the data subject to know that a strong, independent body – which means the ICO – can be trusted to keep watch and offer protection.
With this increase in volume and demand, it’s hardly surprising that the ICO is calling for greater powers, greater independence, and additional funding.
Funding is a particularly difficult area as the EU data protection reforms currently propose the removal of the notification requirement and accompanying fees that fund the ICO’s DPA work. Lack of funding will inevitably give rise to cuts in the services provided by the ICO – for example, it has no legal obligation to provide a helpline, and reduced funding makes it unlikely to be able to continue to handle its current – let alone future – volumes of calls a year.
So it’s absolutely vital not only to individuals but also to businesses, organisations, government and the ICO itself that necessary resource, funding, independence and evolving powers are provided to allow the Information Commissioner to continue to protect, update and enforce data protection legislation.
ICO’s internal data security breach
However, it is somewhat unfortunate that at the time the ICO is asking for greater funding, independence and stronger powers, they are also admitting to their own “non-trivial” data breach. The incident was treated as a self-reported breach and was apparently investigated and treated no differently from similar incidents reported to the ICO by others. After an internal investigation the ICO concluded that the likelihood of damage or distress to any affected data subjects was low, and that it did not amount to a serious breach of the Data Protection Act. A full investigation was carried out with recommendations made and adopted.
However, later information suggests that this breach is now linked to a criminal investigation. So the breach investigation has not, seemingly, been closed.
Data Compliant
If you have any concerns over data protection compliance or security, don’t hesitate to get in touch – call 01787 277742 or email victoria@datacompliant.co.uk

Data Compliance and Cloud Computing
It’s clear that the innovative and accessible technical services provided by cloud computing are increasingly being selected and used by businesses. And there are good reasons for doing so – not least accessibility, cost, reliability, resilience, and innovative products. However, there are also risks to data protection which data controllers need to consider and be sure that such their cloud processing activity complies with the Data Protection Act.
What is cloud computing?
Cloud computing covers a broad range of services and technology, but the Information Commissioner’s Office (ICO) defines it as:
“access to computing resources, on demand, via a network”
To explain:
Resources include storage, processing, software
On Demand simply means that the resources are available to the customer or user on a scalable, elastic basis, typically through virtualised resources
Via a Network refers to the transit of data to and from the cloud provider, which may be over a local or private network, or across the internet.
The Data Protection Act (DPA) and Cloud Computing
All operations involving personal data that take place in the cloud – including storage – must comply with the DPA, and it is the data controller who has ultimate responsibility for that compliance.
However, if layered cloud services are being used (eg different cloud providers of software, platforms or infrastructure) then it’s quite possible that there will be a number of data controllers and data processors working together to deliver services which included processing personal data.
The cloud customer is most likely to be the data controller, and will therefore have overall responsibility for complying with the DPA. However, depending on precisely the role of the cloud provider, the customer must assess whether the cloud provider is simply a contracted data processor or is, indeed, a data controller in its own right – which may be the case if a cloud provider in any way determines the purpose(s) for which the personal data are to be processed. In this case the cloud provider will be responsible for its own data protection compliance.
12 Cloud-specific DPA Considerations
 There are some specific considerations for data controllers who have moved or are considering moving personal data to the cloud. Below are twelve:
There are some specific considerations for data controllers who have moved or are considering moving personal data to the cloud. Below are twelve:
- What personal data is to be processed (and how) in the cloud, and what are the inherent data protection risks
- What steps can be taken to mitigate those risks (eg authorisation protocols)
- Who is the data controller
- What additional personal data may be collected in the cloud (eg usage stats, transaction histories of users and other such ‘metadata’)
- Does the cloud customer’s privacy policy provide adequate information about processing data in the cloud
- Does the cloud customer need to run a privacy impact assessment to identify any privacy concerns and address them from the beginning of the process
- Does customisation of an existing cloud service cause any additional privacy risks
- What monitoring, review and assessment requirements between cloud customer and cloud provider should be put in place to ensure the cloud service runs as expected and to contract
- What commitment does the cloud provider have to keep the cloud customer informed in the event of changes in the chain of sub-processors taking place during the provision of the cloud service
- A written contract is required by the DPA between the data controller and the data processor – beware of a cloud provider which offers terms and conditions with no opportunity for negotiation. The risk that those terms and conditions may subsequently change needs to be taken into consideration.
- The data controller is responsible for the security of its data processor – assessment of the security of the cloud provider is mandatory
- Data outside the UK / EEA – the data controller must check the countries where data is likely to be processed and satisfy itself that the relevant security arrangements are in place
8 Essential Policies and Processes
 Any business will benefit from formal, documented policies and procedures. Having made a decision to use cloud services, there are some specific requirements that are particularly important from a personal data compliance perspective:
Any business will benefit from formal, documented policies and procedures. Having made a decision to use cloud services, there are some specific requirements that are particularly important from a personal data compliance perspective:
- Access control – the data is, by the nature of cloud computing, accessible from any location – home, the office or on a range of devices. Sufficient measures need to be put in place to prevent unauthorised access to the data
- Authentication processes – to verify that a cloud user is authorised to access the data
- A system is required to create, update, suspect and delete user accounts
- Leaver protocols need to be put in place
- Data retention and deletion policies are required – consider your cloud provider’s deletion issues across multiple locations and back-ups
- Cloud provider access policies need to be in place for occasions when the cloud provider needs access in order to provide services
- Staff training on cloud processes and controls is required to maintain the security of the cloud service
- Regular audits of procedures and policies in place will help ensure ongoing compliance
The cloud is here to stay. If you’d like any information or have any concerns about your own cloud provider contracts, policies or compliance issues, please don’t hesitate to contact us:
victoria@datacompliant.co.uk
01787 277742
More delays to the European Data Protection Regulation?
 It is becoming increasingly difficult to say when the European Data Protection Regulation will come into force. The legislation is currently at the point where three-way negotiations need to take place between the Justice and Home Affairs Ministers, the European Commission and the European Parliament to finalise the text . It was broadly anticipated that the draft EU Data Protection Regulation would be passed later this year, making it law in the UK by 2016.
It is becoming increasingly difficult to say when the European Data Protection Regulation will come into force. The legislation is currently at the point where three-way negotiations need to take place between the Justice and Home Affairs Ministers, the European Commission and the European Parliament to finalise the text . It was broadly anticipated that the draft EU Data Protection Regulation would be passed later this year, making it law in the UK by 2016.
However, the recent European elections and new parties now represented in the European Parliament may impact the timescale of the passing of the Regulation and delay it even until early 2015, in which case it would become UK law in 2017. The new Parliament now needs to elect the MEPs to take part in the three-way negotiations, and reappoint members to its various committees etc to reflect the changes in party strength.
One of the interesting issues is that Viviane Reding has just been elected as MEP. In her role as Justice Commissioner, she has been an extraordinary force for the development and implementation of the DP Regulation. But as an MEP she will need to step down from her current role, and there is no guarantee that the new Justice Commissioner will be as driven in terms of getting the legislation passed.
So it is somewhere between difficult and impossible to determine when the European Data Protection Regulation will come into force in the UK, but it is increasingly unlikely to be before early 2017.
What has been clear since March, however, is that the legislation is coming, and businesses will benefit from being ready for the changes that it will bring. If you’d like any help assessing your readiness for the upcoming legislation, please contact Data Compliant on 01787 277742