In today’s digital age, cybersecurity is critical to every organisation’s operations. One of the most common causes of data breaches is when attackers trick you into giving them personal information they should not have.
Vishing and Phishing tricks
For example, through vishing attacks, where somebody calls you and pretends to be a company you work with, and they ask for what seems perfectly reasonable information. You provide it.
Or you click on a link in a phishing email because it looks as though it has come from someone you know. It takes you to a web page asking for information. You provide it.
In both cases, you have provided the attacker with information that should never have been given to them.
What to do next?
These social engineering attempts are becoming increasingly sophisticated, making them hard to detect. And it’s too easy to fall into their trap.
Remember, if you DO click on a malicious link, or enter your password details in a site which looks suspicious …. don’t just pretend it didn’t happen. It is crucial that the error is immediately reported to your line manager or IT department.
Why should I own up to causing a data breach?
Because if you do so immediately, the breach can be prevented. Here’s an example from one of our clients.
One of its employees received an email from a contact he had previously communicated with via a cloud-sharing platform he would normally access, and at first glance, it all looked fine. Until he clicked on a malicious link, entered his credentials and authenticated using Multi-Factor Authentication (MFA). He realised his mistake and reported it to IT immediately.
Here’s what happened

How did reporting it help?
Thanks to the swift reporting and decisive actions taken by the IT team, any potential security breach was thwarted before it could escalate into a more serious incident. There was no breach of confidentiality, inappropriate access, or unavailability of the company’s personal data.
Organisations can prevent potential security breaches and protect their valuable assets by acting swiftly and decisively. Fast action can make all the difference between a minor incident and a significant data breach.
What if I don’t own up?
Well, let’s imagine it. Those login attempts would, without doubt, have succeeded. All the personal data to which that employee had access would be in the hands of the attacker. The company would be facing a severe data breach situation. They’d be using time and resources to investigate. They’d probably be calling in expert help to mitigate the damage. The cost, both in time and money, would be substantial, as they considered:
- How much damage have I done to my customers?
- How can I contain the damage?
- Will I be sued?
- How many customers will I lose?
- Who can I use – internally and/or externally – to help me work through this?
- How much will I have to spend on expert advice and support through the process?
- How will I pay for it?
- Is the breach severe enough to warrant reporting to the supervisory authority – if so, how can I do so within 72 hours?
- How can I save us from the corresponding reputational damage
- How much will I be fined, and what can I do to try to reduce the amount?
But because this issue was reported without delay … none of the above was necessary.
Employers must encourage employees to report errors
Employers play a crucial role in fostering a culture of reporting errors. It is important to create an environment where employees feel safe to admit their mistakes and are encouraged to report any suspicious activity.
So, as an employer, it is your job to make sure your staff know that they must report any errors of this kind. Instead of making them scared to report their mistake, offer them help – for example, by providing additional or repeat training to help them recognise such tricks in future.
Train your workers to stay vigilant, stay informed, and promptly report any suspicious activity to your IT team. This will also have the advantage of fostering a culture of vigilance, awareness and honesty. It helps everyone in the organisation understand the importance of information security and how to safeguard personal data.
If you’re in any doubt, re-read the story above. And stop to think about the potential damage that would have ensued if the individual concerned had not reported his error. The attackers would – without doubt – have logged in successfully, and would then have been able to succeed in meeting their aims – to the detriment of your company and your customers.
Victoria Tuffill
20th August 2024
If you have any questions or concerns with data security and increasing staff awareness, please call 01787 277742 or email dc@datacompliant.co.uk
And please take a look at our services.





 In an historic High Court ruling, the Supermarket has been found liable for Skelton’s actions, which means that those affected may claim compensation for the “upset and distress” caused.
In an historic High Court ruling, the Supermarket has been found liable for Skelton’s actions, which means that those affected may claim compensation for the “upset and distress” caused.




 GDPR Debate
GDPR Debate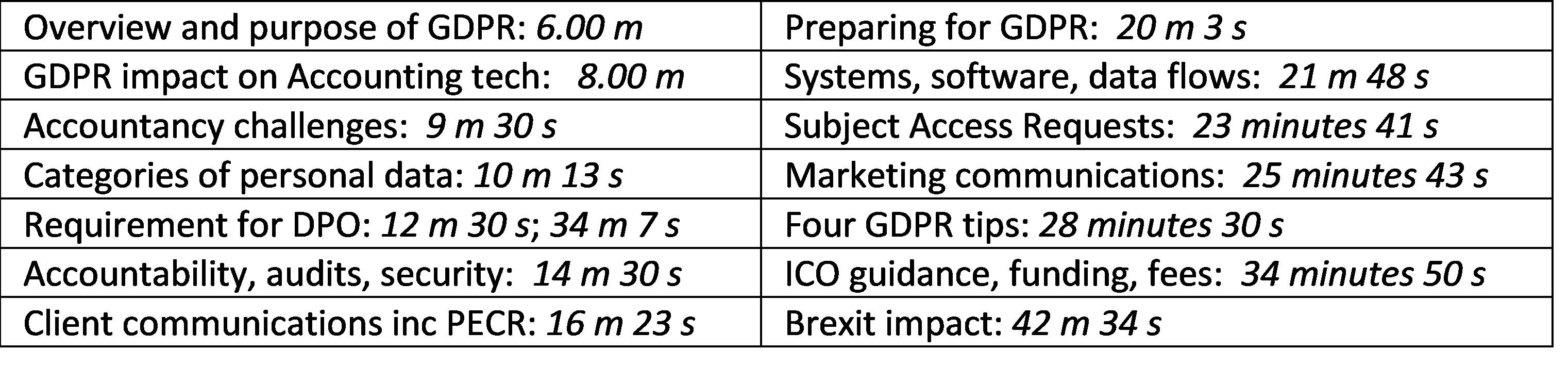 Data Compliant is working with its clients to help them prepare for GDPR, so if you are concerned about how GDPR will affect your firm or business, feel free to give us a call and have a chat on 01787 277742 or email dc@datacompliant.co.uk if you’d like more information.
Data Compliant is working with its clients to help them prepare for GDPR, so if you are concerned about how GDPR will affect your firm or business, feel free to give us a call and have a chat on 01787 277742 or email dc@datacompliant.co.uk if you’d like more information.