Two large corporations fined for PECR breaches; Google study reveals ransomware profits, and Facebook urges people-led changes to security methodology
In the blog below, you’ll note how the Information Commissioner’s Office is taking a hard-line approach to PECR. If an organisation uses electronic channels to re-permission its database in time for GDPR enforcement in May 2018, it must comply with PECR. Moneysupermarket.com is the latest in a series of big names to fall foul of email regulations.
You’ll also see an analysis of ransomware profitability, which helps explain its continued growth; the final story summarises Facebook’s views on data security.
The ICO issues fines amounting to £160,000 for Provident Personal Credit and Moneysupermarket.com
The Information Commissioner’s Office has issued civil monetary penalties of £80,000 each for Provident Personal Credit, a Bradford-based sub-prime lender, and Moneysupermarket.com, a leading brand comparison site, on the 17th and 20th of July respectively. In both cases the fine was for breaching the Privacy and Electronic Communications Regulation (PECR).

Unsolicited texts annoy prospects and customers
Quick-loan credit firm Provident Personal Credit, a brand operated by Provident Financial, was fined £80,000 for sending out nearly 1 million nuisance text messages in the space of 6 months.
The company employed a third party affiliate to send the unsolicited marketing for loans provided by a sister brand, Satsuma Loans.
Text messages may not be sent if the recipients have not consented to receiving marketing texts, so this activity was in breach of PECR.

Beware of sending “service” emails which are actually “marketing” emails
A few days later, the price and brand comparison website Moneysupermarket.com was fined for sending 7.1 million emails over 10 days updating customers with its Terms and Conditions, despite these customers having explicitly opted-out of receiving this type of email. This offence is almost identical to the breaches for which Morrison’s, Honda and Flybe were fined last month.
One of the key problems was the section “Preference Centre Update” which said: “We hold an e-mail address for you which means we could be sending you personalised news, products and promotions. You’ve told us in the past you prefer not to receive these. If you’d like to reconsider, simply click the following link to start receiving our e-mails.”
In a previous blog, we explained the ambiguity between ‘service’ emails and ‘marketing’ emails when implicitly emailing or communicating marketing content to individuals who have opted out. This is in breach of regulations (which will only get stricter after the General Data Protection Legislation comes into force in May 2018).
Google research leads to fears of proliferating ransomware

Ransomware encrypts and scrambles victims’ computerised files. The files will not be decrypted until after a ransom is paid
Research carried out by Elie Bursztein, Kylie McRoberts and Luca Invernizzi from Google has found that cyber-thieves have made $25m (£19m) in the last two years through the use of ransomware. The research suggests that this type of malware regularly makes more than $1m (£761,500) for its creators.
The two strains of ransomware that have seen the most success are ‘Locky’ and ‘Cerber,’ which have collected $7.8m (£5.9m) and $6.9m (£5.2) respectively. But fears have arisen that due to the profitability of ransomware, new and more expansive variants will emerge amid the increasingly competitive, aggressive and “fast-moving” market for cybercrime weaponry. Mr Burszstein warns that ‘SamSam’ and ‘Spora’ are variants that seem to be gaining traction.
The research collected reports from victims of ransomware but also from an experiment wherein thousands of ‘synthetic’ virtual victims were created online. Mr Bursztein and his colleagues then monitored the network traffic generated by these fake victims to study the movement of money. More than 95% of Bitcoin payments (the preferred currency for ransom payments) were cashed out via Russia’s BTC-e exchange.
The lucrative nature of ransomware has led the Google researchers to conclude that it is “here to stay” and may well proliferate among the many syndicates and crime networks around the world. At a talk at the Black Hat conference, one of the world’s largest information security events, Mr Bursztein warned, “it’s no longer a game reserved for tech-savvy criminals, it’s for almost anyone.”
Facebook’s security boss argues that the industry should change its approach

Hitting the data security balance: user issues vs. tech solutions
At a talk at this year’s Black Hat, Facebook’s Chief Information Security Officer, Alex Stamos, has criticised the information security industry’s over-prioritisation of technology over people.
Advocating a ‘people-centric’ approach to information security, Mr Stamos stated his belief that most security professionals were too focused on complex ‘stunt’ hacks involving large corporations and state organisations, and tended to ignore problems that the majority of technology users face.
He told the attendees, “we have perfected the art of finding problems without fixing real-world issues. We focus too much on complexity, not harm.”
He explained that most Facebook users are not being targeted by spies or nation states, and that their loss of control over their information are from simple causes with simple solutions in which, he claims, the security industry takes no interest. He criticised the industry in general for lacking ‘empathy’ with less tech-savvy people, citing the often-expressed thought by security professionals that there would be fewer breaches and data losses if people were perfect.
He used the example of the widespread criticism from cyber experts that the security team for Facebook subsidiary Whatsapp faced after their decision to use ‘end-to-end’ encryption for the popular messaging app, which was heralded by some as sacrificing security for the sake of usability. Such a sacrifice did not manifest, but Mr Stamos was keen to emphasise the fact that it simply did not occur to security experts that usability was worth pursuing.
Mr Stamos advocated the diversification of the industry by working with less technically minded people who could empathise with the imperfections of tech-users, thus helping to develop more straightforward tools and services that would benefit a larger amount of people.
Facebook has also committed half a million dollars to fund a new project to secure election campaigns from cyber attack. The initiative will be run by the Belfer Center for Science and International Affairs, a think-tank affiliated to Harvard University. This is timely, given the scandals around the cyber- attack on French President Emmanuel Macron’s recent election campaign, and the Russian hack of the Democratic National Committee during the US elections last year.
If you have any data privacy compliance, governance or security concerns which you’d like to discuss with Data Compliant, please email dc@datacompliant.co.uk.
Harry Smithson 20th July 2017




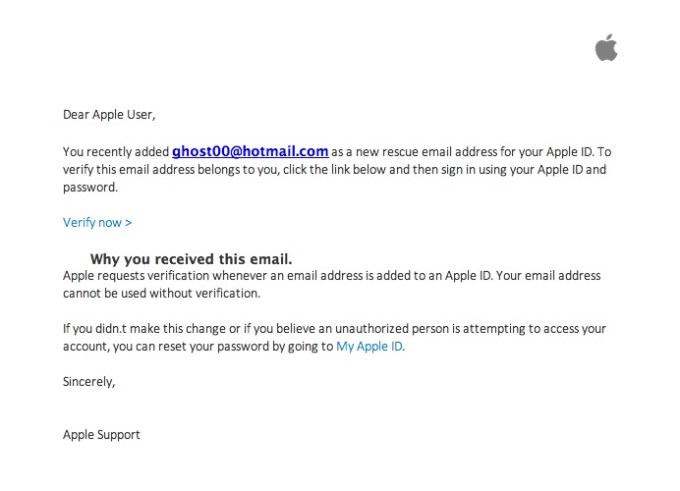
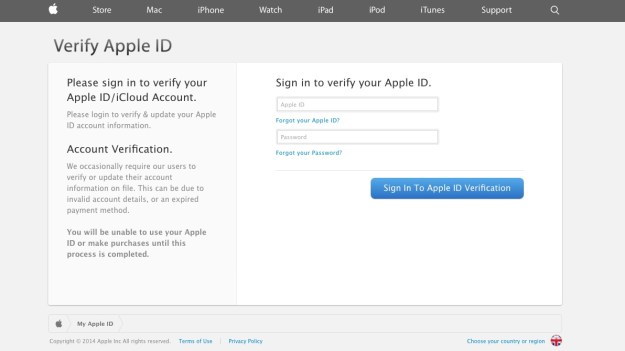
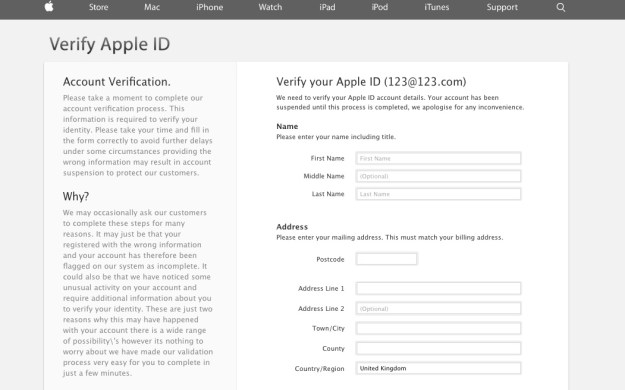
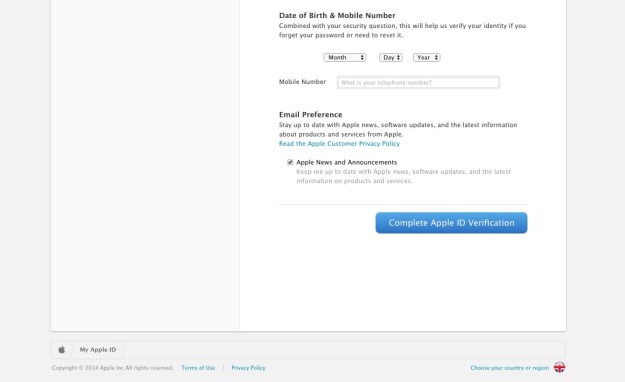
 There I was, at my desk on Monday morning, preoccupied with getting everything done before the Christmas break, and doing about 3 things at once (or trying to). An email hit my inbox with the subject “your account information has been changed”. Because I regularly update all my passwords, I’m used to these kinds of emails arriving from different companies – sometimes to remind me that I’ve logged in on this or that device, or to tell me that my password has been changed, and to check that I the person who actually changed it.
There I was, at my desk on Monday morning, preoccupied with getting everything done before the Christmas break, and doing about 3 things at once (or trying to). An email hit my inbox with the subject “your account information has been changed”. Because I regularly update all my passwords, I’m used to these kinds of emails arriving from different companies – sometimes to remind me that I’ve logged in on this or that device, or to tell me that my password has been changed, and to check that I the person who actually changed it.