Background
On Wednesday 23 October 2024, the UK Government published its Data (Use and Access) Bill (“DUA“). It promised to “harness the enormous power of data to boost the UK economy by £10 billion” and “unlock the secure and effective use of data for the public interest“.
The DUA mirrors many of the concepts and provisions from the previous Government’s abandoned Data Protection and Digital Information Bill (“DPDI“), though there are subtle changes. The DUA appears to place greater focus on data sharing and digital.
It is worth noting that the EU is set to review the UK’s data transfer adequacy status in mid-2025. Maintaining adequacy status is vital to the UK. (Possibly) as a result, some of the more contentious issues included in the discarded DPDI have been removed from the DUA.
With the mid-2025 adequacy review date in mind, the government will undoubtedly try to get the Bill through as quickly as possible. After two readings in the House of Lords, it is now at Committee Stage.
DUA – Key Points for organisations
The key points of the DUA are:
- UK Adequacy Status: As stated above, the EU is reviewing the UK’s adequacy status in Mid-June.
- Accountability requirements: in the DPDI, there were plans to amend and simplify the accountability obligations required under GDPR. These have NOT been carried over into the DUA. Specifically there are to be no changes to:
- the requirements for a DPO
- requirements for Records of Processing Activities
- requirements for Data Protection Impact Assessments.
- ICO Reform: The Information Commissioner’s Office will be replaced by a new corporate body called Information Commission. Executive members will be appointed and scrutinised by the Chair and non-executive members. The Commissioner will be required to look to public interest factors around data protection. For example, it must consider the desirability of promoting innovation and competition. There is also emphasis on protecting children in relation to data processing.
- Special Category Data: the Secretary of State has the power to add and remove new special categories of data. Those that already exist in Article 9 may not be removed.
- Data Subject Access Requests (DSARs): The discarded DPDI inlcuded the concept of an exception around “vexatious” requests. This has NOT been included in the DUA. However, proportionality is a key consideration in the DUA, which makes responding to DSARs more straightforward, including by confirming that a DSAR search for personal data need only be “reasonable and proportionate”
- The 30-day time period to complete a DSAR begins only after the organisation has confirmed the individual’s identity.
- The DUA also helps businesses by turning common DSAR practices, based on ICO guidance, into law.This offers certainty for organisations. For example, where
- If an organisation has large amounts of information about the data subject, it may ask the subject to narrow down the information requested.
- While it seeks this information, it may briefly halt the time frame.
- Legitimate Interests: there is a new concept of recognised legitimate interests where certain data processing activities will not require a full Legitimate Interest Assessment (LIA), specifically, for example:
- safeguarding national security or public safety
- responding to an emergency
- crime prevention / investigation
- public health
- exercising data subject rights, regulatory functions or civil law claims.
- This list can be updated ongoing subject to parliamentary approval.
- It is worth noting that the European Court of Justice has consistently ruled that any interest that is legal may be a legitimate interest – i.e. that a purely commercial interest can be a legitimate interest.
- In addition, when conducting an LIA, it is acceptable to take into account not only the benefits to the individuals, but also so the environment (e.g. paper reduction), economy (e.g. generating growth and spending budgets in a targeted manner).
- Privacy and Electronic Communications Regulations: PECR is included in DUA, and therefore is aligned with the levels of fine available for GDPR breaches. This is a massive increase from the £500,000 maximum fine currently in place. In addition, the DPDI’s email soft opt-in for non-commercial organisations (such as charities) is NOT currently included (though lobbying is ongoing).
- Cookie Consent Exemptions: The aim is to reduce the number of cookie consent banners. DUA allows the use of cookies without consent in specific circumstances, such as ensuring security or preventing fraud, collecting information for statistical purposes for own use, to improve the website functionality and appearance to the user, and to provide emergency assistance. This is particularly beneficial to those parties who do not use advertising cookies – for example B2B websites.
- Digital Verification Services: DUA aims to create a framework for trusted online identity verification services, moving away from paper-based and in-person tasks (e.g. registering births and deaths online). Companies providing digital verification tools must be certified against government standards and will receive a ‘trust mark’.
- Smart Data Schemes: The introduction of smart data schemes will require businesses in sectors like financial services and public utilities to enable data interoperability and secure data sharing. This aims to enhance consumer confidence and drive innovation
- Data Access Provisions: The DUA introduces data access standards similar to the EU’s Data Governance Act, enabling controlled data sharing between businesses and public authorities.
- Automated Decision Making: The DUA will make it easier for organisations to adopt a broader use of automated decision-making for low-risk, beneficial processing – for example when using artificial intelligence (AI) systems. It limits the scope of the UK’s GDPR Article 22 to cover only “significant” decisions, and those based either in part or entirely on special category data.
- Data Transfers: the DUA replaces Chapter 5 of the UK GDPR with a new “data protection test” for the Secretary of State to consider international data transfers, in which the objective is to ensure standards are not materially lower than in the UK. This differs from the EU approach which looks for equivalence.
Timetable
With the upcoming adequacy review in mind, it seems likely that the government is trying to get the Bill through as quickly as possible – it has already had two readings in the House of Lords and is currently at Committee Stage in the House of Lords.
Data Compliant
If you would like help or assistance with any of your data protection obligations, please email dc@datacompliant.co.uk or call 01787 277742, And, for more information about to meet your accountancy obligations – both before and after the DUA comes into force, please see here.
Victoria Tuffill
18th December 2024



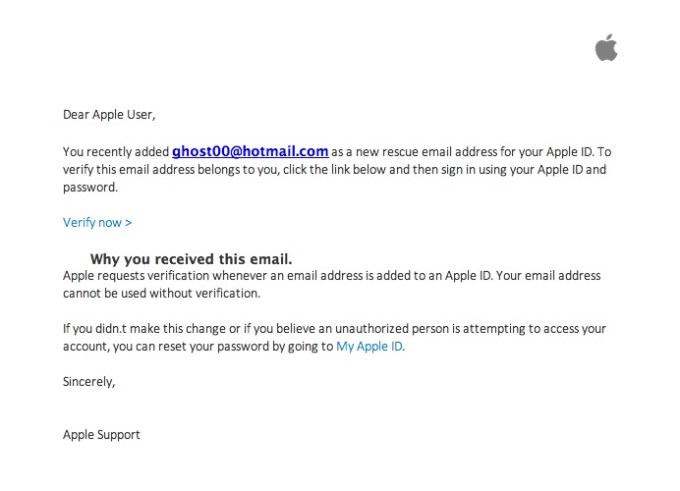
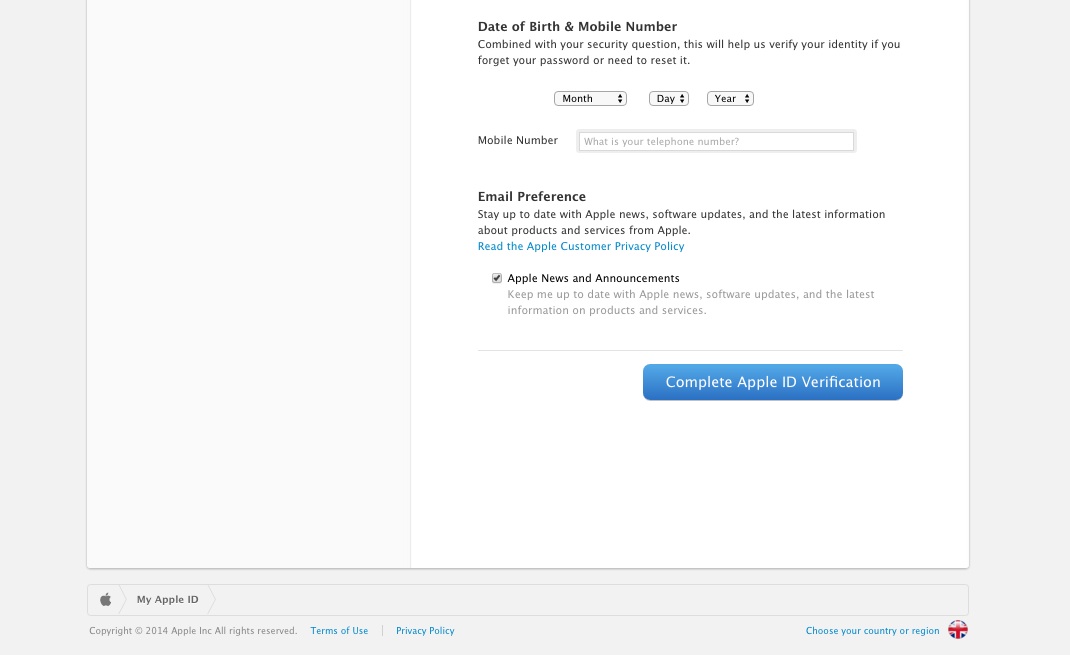
 There I was, at my desk on Monday morning, preoccupied with getting everything done before the Christmas break, and doing about 3 things at once (or trying to). An email hit my inbox with the subject “your account information has been changed”. Because I regularly update all my passwords, I’m used to these kinds of emails arriving from different companies – sometimes to remind me that I’ve logged in on this or that device, or to tell me that my password has been changed, and to check that I the person who actually changed it.
There I was, at my desk on Monday morning, preoccupied with getting everything done before the Christmas break, and doing about 3 things at once (or trying to). An email hit my inbox with the subject “your account information has been changed”. Because I regularly update all my passwords, I’m used to these kinds of emails arriving from different companies – sometimes to remind me that I’ve logged in on this or that device, or to tell me that my password has been changed, and to check that I the person who actually changed it.