Meanwhile, back in the UK …
 Telemarketing – Caller identification spoofing …
Telemarketing – Caller identification spoofing …
Earlier this week, Canada, the United States and the United Kingdom issued a joint statement making it clear that they intend to combine their resources to tackle the problem of caller ID spoofing.
Spoofing is a practice conducted by telemarketers who want to conceal their true identity rather than fulfil their legal obligation to identify themselves. Spoofers provide their caller ID with false information which may be a string of digits, or a random or stolen number belonging to a real person or organisation. It is on the increase, and makes it particularly difficult for the authorities to track down those responsible for non-compliant or illegal calls.
The various agencies responsible for enforcing telemarketing and privacy laws announced that they will coordinate their efforts through the international law enforcement network of the London Action Plan and the International Do Not Call Network. If they need the telecoms industry to provide help, they will ask those organisations within their respective countries.
Next steps are exploratory discussions, to be held later this month, to identify options focusing on enforcement, industry compliance and consumer education, technology and regulatory issues with the goal of considering solutions available to stop spoofing and to take action against those responsible.
DATA BREACHES AND FINES
What a monumental blunder …
 We heard yesterday that The Ministry of Justice was on the receiving end of the ICO’s judgement, when it received a fine of £140,000 – after details of ALL the prisoners serving time at HMP Cardiff were emailed to three of the inmates’ families.
We heard yesterday that The Ministry of Justice was on the receiving end of the ICO’s judgement, when it received a fine of £140,000 – after details of ALL the prisoners serving time at HMP Cardiff were emailed to three of the inmates’ families.
The fine goes back to 2011 – when, on 2nd August, the recipients received an email from a prison clerk which included a file containing details of the 1,182 inmates – including names, ethnicity, addresses, length of sentence, release dates, and the offence codes. Worse yet – this wasn’t the first time such a breach had occurred. Within the previous four weeks, the same error occurred twice – with details sent to different inmates’ families.
The ICO’s investigation found:
- Clear lack of management and supervision at the prison, where the clerk concerned was found to have received limited training and experience, though he was left to work unsupervised.
- Audit trails were lacking and the only reason the breach was identified was because one of the recipients reported receipt of the information to the prison.
- Problems with the methods used to handle the prisoners’ records, such as the use of unencrypted floppy discs to transfer large volumes of data between networks
The importance of being registered …
 If organisations process personal data, with a very few exceptions, they must register with the ICO and spell out the type of information they process. Not doing so is a criminal offence – as Hamed Shabani, sole director of payday loan company First Financial, discovered.
If organisations process personal data, with a very few exceptions, they must register with the ICO and spell out the type of information they process. Not doing so is a criminal offence – as Hamed Shabani, sole director of payday loan company First Financial, discovered.
After failing to register, he and his company were prosecuted by the ICO and convicted in the Magistrate’s Court. As Director of the company, he was fined a modest £150 and ordered to pay £1,010.66 towards the costs of prosecution and a £20 victims’ surcharge. In addition, the company itself was fined £500, and also made to pay £1,010.66 towards costs plus a £50 victims’ surcharge.
The total bill of £2,741.32 compares rather unfavourably against the annual £35 notification fee he should have paid. It is also interesting to note that Hamed Shabani tried to remove his name from the company’s registration at Companies House in an attempt to avoid prosecution.
To quote Stephen Eckersley, ICO Head of Enforcement:
“Pay day loans companies hold important information about some of the most financially vulnerable people in the UK. This makes this company and its director’s decision not to face up to their legal responsibilities all the more concerning.
“Businesses must commit to looking after the information of their customers and this begins with making sure that they are registered. We will continue to use our enforcement powers to safeguard people’s information.”
The importance of a strong BYOD policy …
 BYOD (Bring your own device) continues to be high on the ICO’s priority list – earlier this month, the Royal Veterinary College breached the DPA when a member of staff lost their camera whose memory card held 6 job applicant passport pictures. Unfortunately, the RVC had not briefed staff on how personal information stored for work should be looked after on personal devices.
BYOD (Bring your own device) continues to be high on the ICO’s priority list – earlier this month, the Royal Veterinary College breached the DPA when a member of staff lost their camera whose memory card held 6 job applicant passport pictures. Unfortunately, the RVC had not briefed staff on how personal information stored for work should be looked after on personal devices.
Nearly half of all UK employees now use their smartphones, tablets, PCs for work purposes, and the number is growing. As a result, organisations must update their data protection policies to take this into account.
Stephen Eckersley said:
“Organisations must be aware of how people are now storing and using personal information for work and the Royal Veterinary College failed to do this. It is clear that more and more people are now using a personal device, particularly their mobile phones and tablets, for work purposes so its crucial employers are providing guidance and training to staff which covers this use.”
The importance of encryption …
 If you are unlucky enough to have a portable device containing personal data stolen, it could cost you much more than simply replacing the device. As the owner of loans company Jala Transport discovered to his cost. He stopped his car at a set of traffic lights, only to have his car boot broken into. A hard drive – containing financial details of his 250 customers – was stolen, along with £3,600 cash.
If you are unlucky enough to have a portable device containing personal data stolen, it could cost you much more than simply replacing the device. As the owner of loans company Jala Transport discovered to his cost. He stopped his car at a set of traffic lights, only to have his car boot broken into. A hard drive – containing financial details of his 250 customers – was stolen, along with £3,600 cash.
Though the hard drive was password protected, the data within was not encrypted, and it included customers’ names, dates of birth, the payments made, and the identity documents provided to support the loan application. Because the hard drive had not been encrypted, all those customers were left wide open to the threat of identity theft.
The penalty could have been £70,000, but was reduced to £5,000 to reflect the limited financial resources of the company and the fact that the breach was reported voluntarily.
Stephen Eckersley said of this case:
“We have continued to warn organisations of all sizes that they must encrypt any personal data stored on portable devices, where the loss of the information could cause clear damage and distress to the customers affected…
“The penalty will have a real impact on this business and should act as a warning to all businesses owners that they must take adequate steps to keep customers’ information secure.”
Rates of identity fraud continue to rise
Identity fraud is the most significant threat facing the UK, making security a key issue not only for businesses but also for individuals. Not taking steps to protect personal data just gives fraudsters a license to steal. This is clearly illustrated by the stats – identity fraud now accounts for over half of all committed fraud and is still growing. CIFAS confirmed 114,000 frauds in the first half of 201, of which 52% involved impersonation or fake identity details. An additional 14% of frauds involved account takeover.
All the stories above reflect the importance of being and remaining data compliant and illustrate the penalties that can be imposed by the ICO. If you would like any advice on how to become and remain compliant, just call us for a no-obligation chat.

- Victoria Tuffill
01787 277742
victoria@tuffillverner.co.uk

- Michelle Evans
01206 392909
michelle@tuffillverner.co.uk
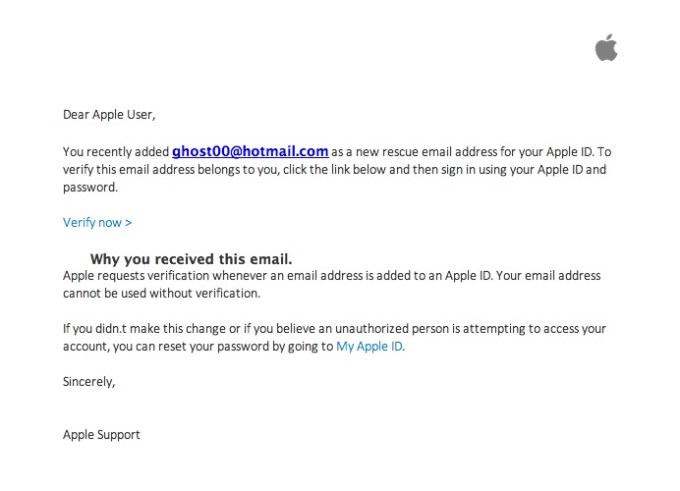
 There I was, at my desk on Monday morning, preoccupied with getting everything done before the Christmas break, and doing about 3 things at once (or trying to). An email hit my inbox with the subject “your account information has been changed”. Because I regularly update all my passwords, I’m used to these kinds of emails arriving from different companies – sometimes to remind me that I’ve logged in on this or that device, or to tell me that my password has been changed, and to check that I the person who actually changed it.
There I was, at my desk on Monday morning, preoccupied with getting everything done before the Christmas break, and doing about 3 things at once (or trying to). An email hit my inbox with the subject “your account information has been changed”. Because I regularly update all my passwords, I’m used to these kinds of emails arriving from different companies – sometimes to remind me that I’ve logged in on this or that device, or to tell me that my password has been changed, and to check that I the person who actually changed it.