As part of several of measures aimed at “making our country safer and more united,” a new Data Protection Bill has been announced in the Queen’s Speech.
The Bill, which follows up proposals in the Conservative manifesto ahead of the election in June, is designed to make the UK’s data protection framework “suitable for our new digital age, allowing citizens to better control their data.”
The intentions behind the Bill are to:
- Give people more rights over the use and storage of their personal information. Social media platforms will be required to delete data gathered about people prior to them turning 18. The ‘right to be forgotten’ is enshrined in the Bill’s requirement of organisations to delete an individual’s data on request or when there are “no longer legitimate grounds for retaining it.”
- Implement the EU’s General Data Protection Regulation, and the new Directive which applies to law enforcement data processing. This meets the UK’s obligations to international law enforcement during its time as an EU member state and provides the UK with a system to share data internationally after Brexit is finalised.
- To update the powers and sanctions available to the Information Commissioner.
- Strengthen the UK’s competitive position in technological innovation and digital markets by providing a safe framework for data sharing and a robust personal data protection regime.
- Ensure that police and judicial authorities can continue to exchange information “with international partners in the fight against terrorism and other serious crimes.”
Ultimately, the Bill seeks to modernise the UK’s data protection regime and to secure British citizens’ ability to control the processing and application of their personal information. The Queen’s Speech expressed the Government’s concern not only over law enforcement, but also the digital economy: over 70% of all trade in services are enabled by data flows, making data protection critical to international trade, and in 2015, the digital sector contributed £118 billion to the economy and employed over 1.4 million people across the UK.
Written by Harry Smithson, 22nd June 2017


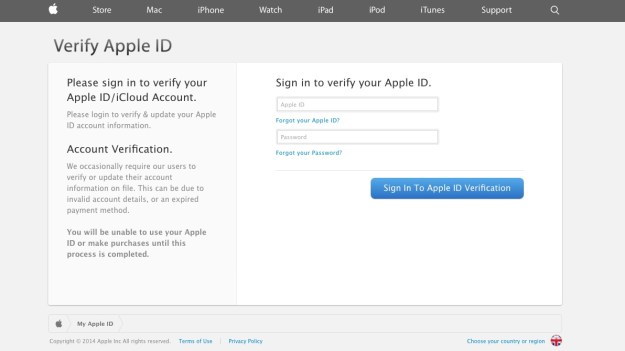
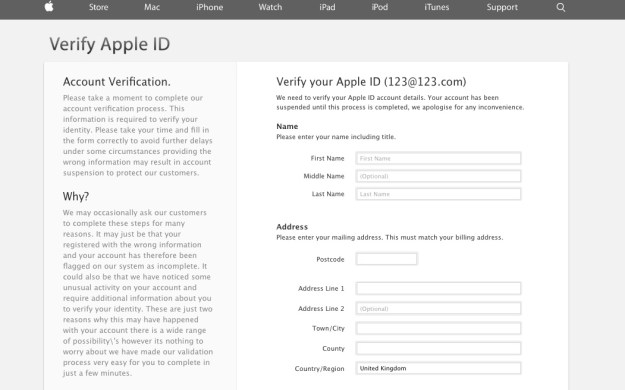
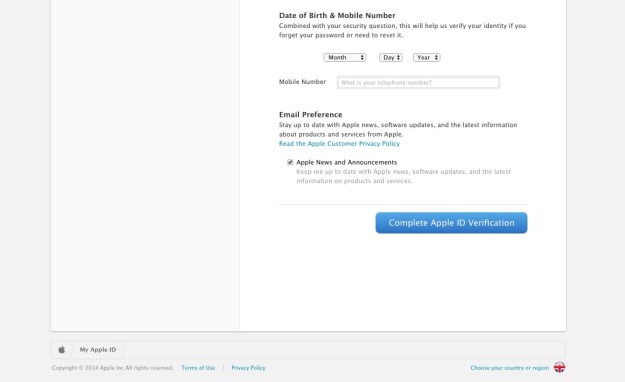
 There I was, at my desk on Monday morning, preoccupied with getting everything done before the Christmas break, and doing about 3 things at once (or trying to). An email hit my inbox with the subject “your account information has been changed”. Because I regularly update all my passwords, I’m used to these kinds of emails arriving from different companies – sometimes to remind me that I’ve logged in on this or that device, or to tell me that my password has been changed, and to check that I the person who actually changed it.
There I was, at my desk on Monday morning, preoccupied with getting everything done before the Christmas break, and doing about 3 things at once (or trying to). An email hit my inbox with the subject “your account information has been changed”. Because I regularly update all my passwords, I’m used to these kinds of emails arriving from different companies – sometimes to remind me that I’ve logged in on this or that device, or to tell me that my password has been changed, and to check that I the person who actually changed it.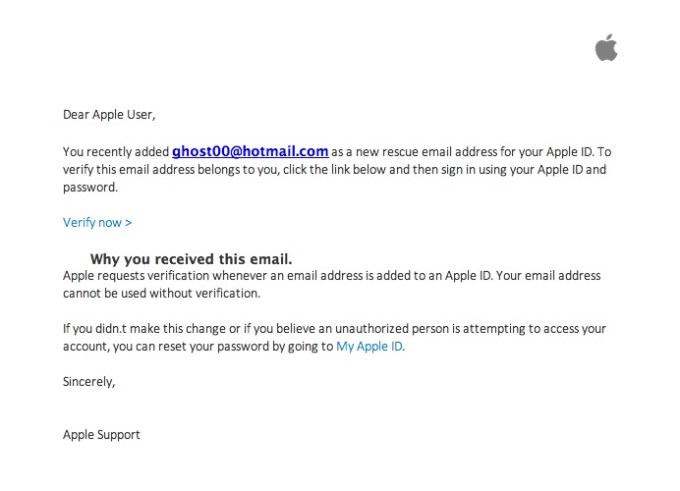






 The Investigatory Powers Bill, also known as the Snoopers’ Charter, was passed by the House of Lords last week. This means that service providers will now need to keep – for 12 months – records of every website you visit, (not the exact URL but the website itself), every phone call you make, how long each call lasts, including dates and times the calls were made. They will also track the apps you use on your phone or tablet.
The Investigatory Powers Bill, also known as the Snoopers’ Charter, was passed by the House of Lords last week. This means that service providers will now need to keep – for 12 months – records of every website you visit, (not the exact URL but the website itself), every phone call you make, how long each call lasts, including dates and times the calls were made. They will also track the apps you use on your phone or tablet.


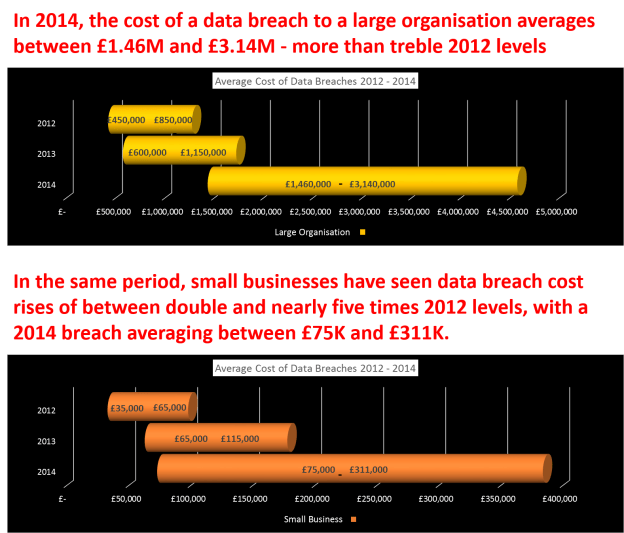
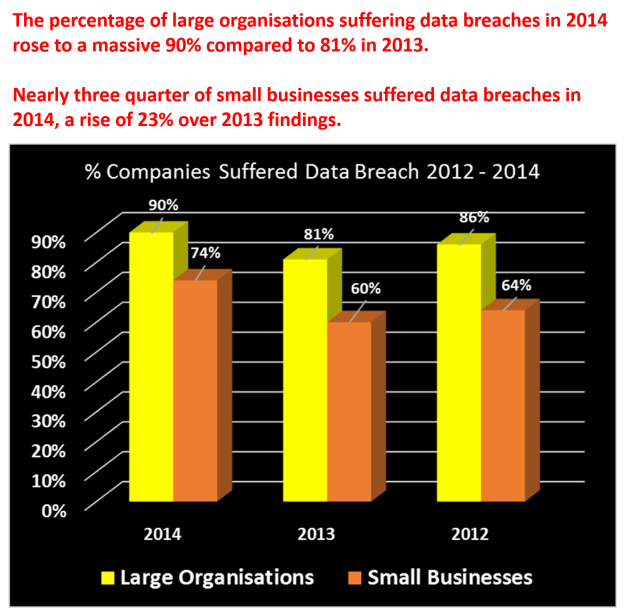
 It is widely known that hackers target all companies large or small. In social media and cloud storage terms, we’ve seen breaches from a range of businesses include MySpace, LinkedIn, to DropBox and many more.
It is widely known that hackers target all companies large or small. In social media and cloud storage terms, we’ve seen breaches from a range of businesses include MySpace, LinkedIn, to DropBox and many more.
 At last agreement has been reached on the EU – US Privacy Shield agreement which now replaces the Safe Harbor agreement. Safe Harbor was ruled invalid in 2015 by the EU Court of Justice, because they said there were not sufficient safeguards for personal data under the voluntary scheme.
At last agreement has been reached on the EU – US Privacy Shield agreement which now replaces the Safe Harbor agreement. Safe Harbor was ruled invalid in 2015 by the EU Court of Justice, because they said there were not sufficient safeguards for personal data under the voluntary scheme.